Delve conveniently brings together colleagues and content related to you and your work. With new Item Insight settings, we have more control over Delve’s privacy and security.
More than once, I’ve had to convince Delve’s safety to my customers. Delve is a Microsoft 365 workload providing each user with a personal profile page and a view of their organization’s documents and users. Delve interface is familiar to users of various social media. Although my customers’ concerns with Delve have not always been based on real life, I have not been able to absolve all the concern.
In certain specific situations, such as trade union activity at the workplace or counseling, Delve may reveal too much information about who is dealing with whom. Following the updates published in June 2021, Delve is now improving in this respect and there is less cause for concern again.
Delve is, as the name suggests, *digging into* organizations’ information in Microsoft 365. Delve’s engine is the Office Graph, continuously collecting and analyzing signals from users’ actions within a Microsoft 365. Office Graph is a somewhat difficult entity to define. It has evolved since the release of Delve in 2014 and according to Microsoft’s recent documentation, Office Graph is essentially a code name for services and analytics built on top of an infrastructure created by the FAST Office Graph Team.
The exact structure of Office Graph is a trade secret and intellectual property of Microsoft. It has been hard to find up-to-date information about it. Office Graph is a graph database, i.e., based on nodes and relations, and as such, it is very well suited for processing complex data, such as describing relationships between individuals and the documents they handle. A similar data structure is leveraged by many social media services, such as Facebook, for example.
When a Microsoft 365 user views or edits a file and their peers do the same, with the same file, a signal of their collaboration is created and stored in Office Graph. Signals also arise about who they email or share files with, who is a manager, who has the same manager and so on. The analysis and utilization of signals in Delve is based on machine learning algorithms, i.e., artificial intelligence. These algorithms are also Microsoft’s trade secrets as well.
Microsoft Graph (API) is a REST interface for all Microsoft 365 workloads, such as SharePoint, Teams, Planner, OneNote, Outlook, Microsoft Search and Windows 10, Azure Active Directory, et cetera. Microsoft Graph utilizes Office Graph by exposing interfaces to it. For example, it is possible to programmatically utilize “trending” content signals stored in the Office Graph by querying Microsoft Graph API. Unlike Office Graph, Microsoft Graph is well-documented and exploitable.
Delve and security
Typical Delve concern (also known as “Delve panic”) occurs soon after an organization rolls out Microsoft 365 to the whole organization. For example, this can happen, when a new intranet on SharePoint Online is launched and a wider audience becomes interested in Microsoft 365. In this scenario, someone in the top management, concerned that Delve reveals confidential information not intended for the entire organization, contacts the IT department and dictates shutting down of Delve.
Display of confidential documents in Delve is of course true, but what it is generally disregarded in such panic, is that the Delve experience is personalized for every user. Delve does not alter the permissions or access to documents or any other information. Through Delve users can only find information that they already have been given access to. From a security point of view, Delve is by no means the cause of the problems, but it may reveal security-related deficiencies by making information more discoverable. It would be available without Delve too. Just not that easily.
Delve and privacy
Delve confidentiality and data protection are another story. Delve utilizes data from all Microsoft 365 workloads and Azure AD. In between Delve and the information are the secret algorithms and the Office Graph.
Delve is therefore just an interface that can be turned off. This would have no effect on data being collected in background systems. Microsoft 365 and Delve comply to regulation (e.g., EU model clauses) but its data processing transparency is impaired by design.
Data protection issues with Delve are tangible in use cases like the ones mentioned at the beginning of this text. There are people in organizations, who are usually contacted only in very confidential matters. Contactors, nor the organization, do not want these connections revealed.
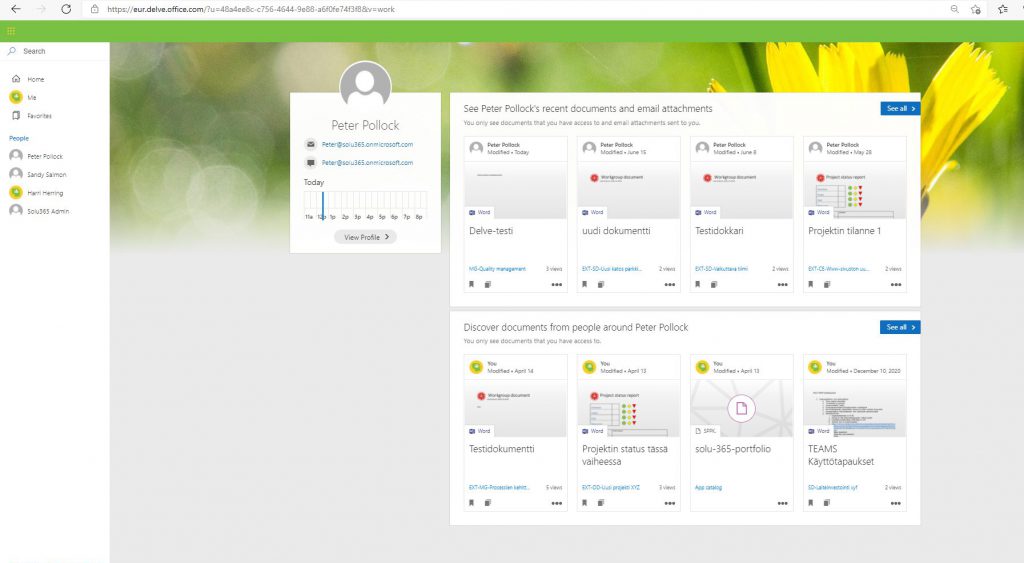
The fact that Harri Herring and Peter Pollock have been involved with each other is evident on Peter Pollock’s Delve page. “You only see documents that you have access to, and emails attachments sent to you.” So it is, but the fact that documents handled by Harri appear on Peter’s Delve page in the first place, may be revealing too much information.
Turning off Delve
Due to Delve-related issues, some organizations have ended up not deploying, or rather, excluding Delve shortly after the intranet launch or similar event. In the past, turning off Delve introduced some additional changes in user experience, such as hiding recommended SharePoint sites, recommended content on the Outlook mobile interface, recommended documents on the Microsoft Office home page, and so on.
As of July 1, 2021, switching off Delve with a control found in the classic SharePoint admin portal will no longer affect Delve’s backend systems, but only Delve’s user interface instead. In other words, turning off Delve will no longer solve the privacy issue that may be associated with Delve.
Delve can be switched off or on by personally. The feature named Property Settings can be found on the Delve page behind the gear icon. If you turn off Delve, other users will still find the files in Office 365 if they have access to them. The files just don’t appear in Delve anymore.
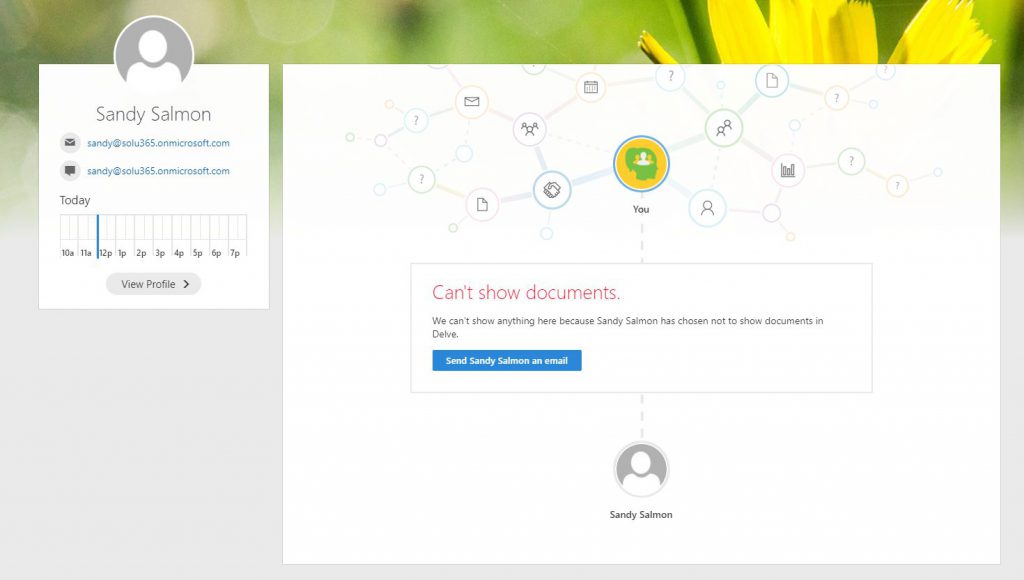
Sandy’s Delve page looks like this as soon as Sandy has changed Delve property settings so that displaying files in Delve is turned off. Sandy also doesn’t see the documents that appear on other users’ Delve page, even if they still have Delve on.
In this case too, disabling Delve restricts only the viewing of documents through Delve. Other insights driven views that were previously controlled with Delve setting, remain visible.
Item Insights
In June 2021, Microsoft released the preview version of Item Insights control for administrators. A similar control was published previously for all users, allowing them to toggle collection of signals from documents to be stored in Office Graph. In other words, this control lets users decide whether Office Graph collects signals from documents they have handled, or not.
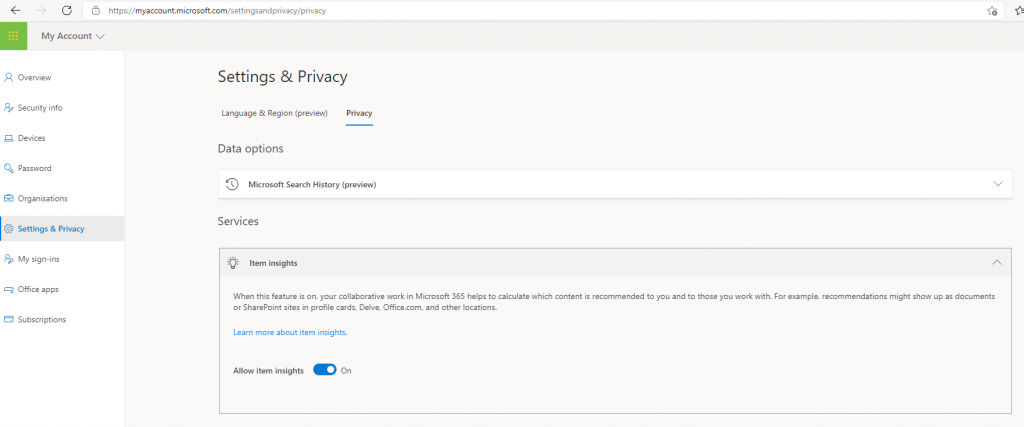
The self-service privacy control can be found in Microsoft 365 account Settings and Privacy view, under Privacy, by the name Item Insights.
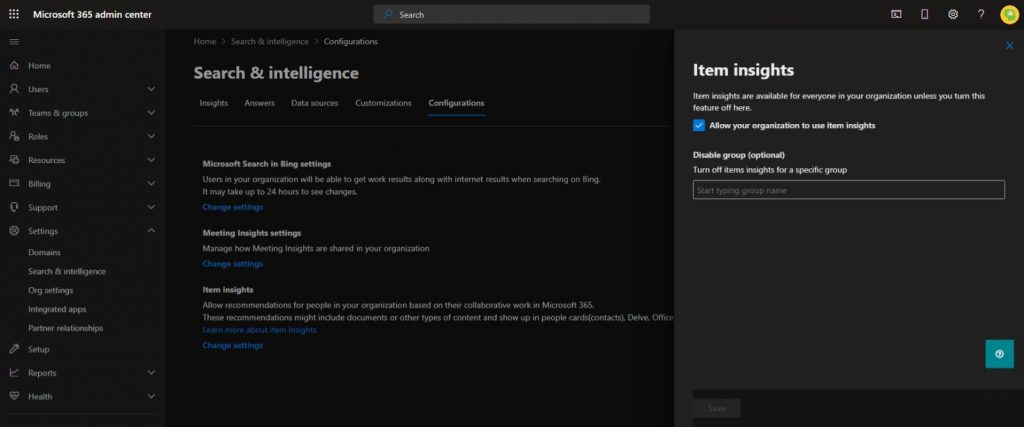
The administrators’ Item Insights control can be used to close signals to all users or a specific Azure AD user group.
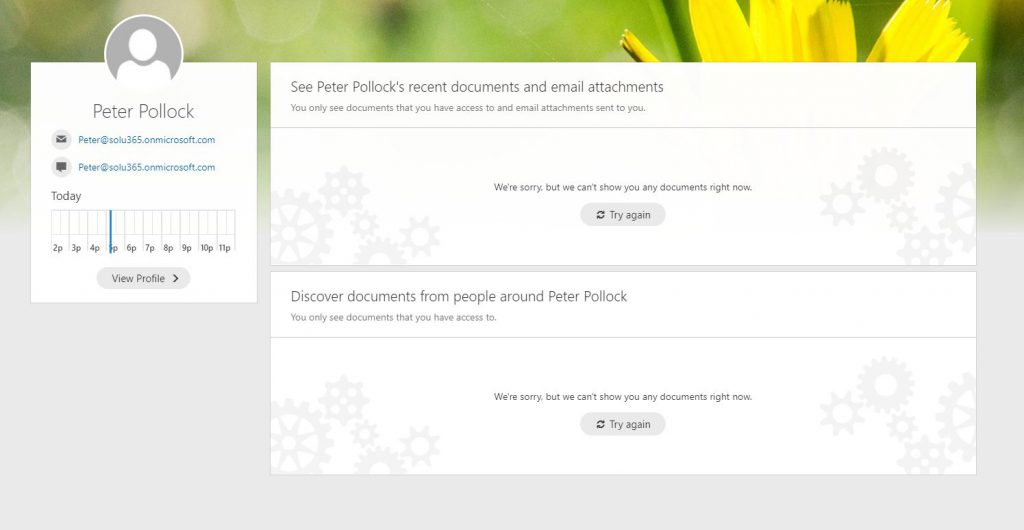
Peter has turned off detection and analysis of items related signals in the Settings and Privacy view of his Microsoft 365 account. Peter still sees other users’ recommended documents in Delve and other insights-driven views.
In contrast to filtering just the user interface by closing Delve, Item Insights control prevents signals between users and documents from being stored in Office Graph in the first place and restricts Microsoft Graph API interface end points as well.
Microsoft Graph API resource itemInsightsSettings controls the visibility and computing of item and meeting insights. It is still in the beta version of the API, but it is likely to be in production soon because the corresponding graphical user interface controls in the Microsoft 365 management portal are already generally available.
Item Insights is the right tool for controlling Delve’s data protection. Organizations that have previously shut down Delve should change their settings, so the restriction is applied with Item Insights to the signals collected in the background, rather than to Delve’s user interface alone.
Control over Delve is not necessary in most organizations. Restricting Item Insights is worth considering and needs some planning in advance, as changes to the settings may take up to a week to come into force. Whether controlling Item Insights is deemed necessary at the level of the users, groups, or the whole organization, varies case by case.
Henry Scheinin
Leading consultant, partner








